After the April raid on my property in Orange Walk I went on the offensive. I had asked for a simple apology and had received none. I was pissed. They had shot my dog, destroyed my property and stolen hundreds of thousands of dollars worth of things that I valued. They have still not been returned.
I purchased 75 cheap laptop computers and, with trusted help, installed invisible keystroke logging software on all of them – the kind that calls home (to me) and disgorges the text files. It also, on command, turns on, and off, the microphone and camera – and sends these files on command. I had the computers re-packaged as if new. I began giving these away as presents to select people – government employees, police officers, Cabinet Minister’s assistants, girlfriends of powerful men, boyfriends of powerful women. I hired four trusted people full time to monitor the text files and provide myself with the subsequent passwords for everyone’s email, Facebook, private message boards and other passworded accounts. The keystroke monitoring continued after password collection, in order to document text input that would later be deleted. So nothing was missed…
I next collected my human resources for the complex social engineering I would have to do. I arranged with 23 women and 6 men to be my operatives. Eight of the women were so accomplished that they ended up living with me. It was amazingly more efficient and they were easily convinced to check up on each other. One was so accomplished (Marcia) that she became a double agent and nearly got me killed:
story from post3 and story from post4
These men and women were given simple training on how to access and load software on someone’s computer while they slept, or ate or made long phone calls etc. It’s dead simple if you’re sleeping with someone – “Hey Babe, can I borrow your computer to check my email?” – A little more complex if you’re not – but not much. They were also shown dirt simple phone tricks, like borrowing a person’s phone to make a call and then resetting auto-delete of sent texts. No-one ever checks these things after setup, so all the sent texts are now available to the person borrowing your phone to call their boyfriend to make up a story so they can sleep over with you. Due to the nature of the call, the operative clearly needed privacy during the call – hence ease of access to changing your settings and reading your sent texts
And I taught them other tricks.
When my teams were assembled, I targeted the two National phone companies for engineering. It was imperative for me to be able to hear people’s phone conversations, or at the very least to know with whom they were in contact. This social engineering exercise was the easiest. I used myself as the decoy in this operation.
I approached numerous employees of both companies with the offer to buy the information that I needed. I knew this would raise flags and lead to failure. I did this in a manner that would not get me arrested but would ensure that my enquiries reached the appropriate ears – ears belonging to people who definitely did not want me to learn anything. People then knew I was after information and, as they would naturally think, I would use “buying” as my technique. Both companies eventually gave me information, which I purchased, but it was, as expected, garbage. While I was negotiating all of this, my team was working its way through the lower ranks of Phone Company employees and had locked onto a number of key players who had access to the technical processes involved in tapping phones and delivering lists of phone contacts. The team had contact information for appropriate wives and husband of these key players, knew the names of the employees’ drug providers (if any), names of respectable family members, and names of all the other “side interests” of the targets. Being “pillow talk” masters, they also knew, and had verified, every secret thing the persons had ever done. Phone Project complete.
Simultaneously with the above, I had identified key “helpers” for each Government Minister and had sent in social engineers to stroke the helpers. Each was armed with software, presents, a story, a seductive smile and a small voice recorder. Everyone had at least one voice recorder. They were small. They could be hidden under a bed, behind a piece of artwork, inside a pillow, in an old shoe. They could be kept on, recording, for days on end prior to retrieval.
Throughout this process I emailed the Prime Minister every few weeks and asked for an apology. A simple apology, in the early stages at least, would have stopped this whole affair. I received none.
What I was looking for was hard proof of corruption at a high level. I’m not sure what I expected to gain. The satisfaction of revenge perhaps – to some extent – what little satisfaction there is in revenge. As a way to get my stuff back? Maybe. For the sheer joy of muscle flexing? I can’t answer precisely. Much of my life is a mystery to me. Suffice it to say: I just did it because I could.
What I found was, for the most part, expected — Uncountable numbers of sexual affairs — Embarrassingly lurid and intimate chats — Multiple, simultaneous protestations of love, and jealousy and anger.
Some things were surprising. I kept sending increasingly irresistible women in the direction of the UDP Party Chairman, to absolutely no avail. Finally, a clever but unsuccessful young woman suggested an alternate chromosome configuration and – success at last. It was a surprise to me, given the macho nature of the Chairman.
I was also surprised that the Prime Minister had personally ordered the murder of Arthur Young. I had assumed that the idea came from much lower in the ranks. But other than these few and other not so remarkable bits of information, things fell pretty much into the order that I had anticipated. There were a few exceptions. This one comes to mind, and it proved to be central to an issue I had anticipated:
While monitoring a young woman working in the Ministry of Immigration, whose Facebook chats had always been exclusively in Creole, the following popped up:
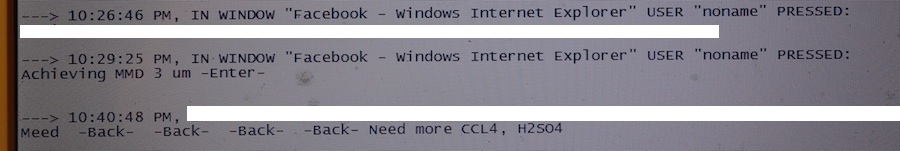
She was chatting on Facebook at the time with another young woman who had a limited education. This occurred in late May. The person monitoring the computer keystrokes forwarded it to me. I sent a command to the system to activate the camera every 10 minutes and send me still shots. After two days of monitoring nothing showed up other than the woman’s face that used the computer. I managed to compromise the computer used by the friend she was chatting with and activated both the camera and the microphone on her system, but again, nothing showed up. I finally sent in a human resource. More on this later.
I had early on documented heavy human trafficking as part of the National Security and Immigration Ministries’ activities. This was hardly news, however. All over Belize are huge billboards pleading for the cessation of human trafficking, much as billboards in America used to beg us not to drink and drive. Everyone knew it was happening – obviously. The billboards weren’t for nothing. So my discoveries were uninteresting old news.
However, in the Belizean catchall “human trafficking” was an interesting statistic that I uncovered: Nearly 25% were Lebanese, and all of these were male. The entry passports for these Lebanese varied – Jordanian, Afghani, Saudi Arabia – but they nearly all spoke Lebanese Arabic. The Lebanese were handled differently. A false identity was created using a deceased Belizean with an appropriate English or European sounding name. For example:
Who helped Hezbollah terrorist get Belizean passport&IDs
After the false Identity was created a passport was issued (this, by law, takes five years of residency, but remember, this whole thing was created and run by the Government – so sidestepping the law is trivial). After the passport was issued, a handler was assigned to help the person exit Belize safely and arrive in America safely (safe for them that is. Not so safe for America). This was accomplished by turning the person in question over to a different, sequential set of handlers along the way. The Architect of this process is John Saldivar – Minister of National Security, and for a while, Minister of Immigration as well.
I had located an individual working in Immigration that was trustworthy and willing to talk. I discovered that an average of eleven Lebanese males were given new identities each month. One month there were sixteen:
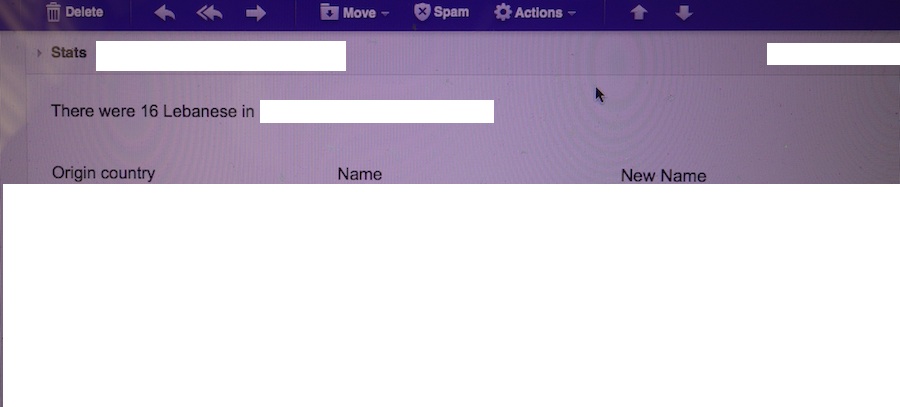
I have redacted the original, and new names, for obvious reasons.
The human resource I sent to check on the odd sequence of texts from late may reported a surprising piece of information: A young gentleman named Farid had taken up with the woman from Immigration whose computer he used (this is a different woman from the one who sent me monthly statistics). My resource, being more clever than the average Belizean young woman, quickly snaked Farid for herself. Early on I received this email from her:
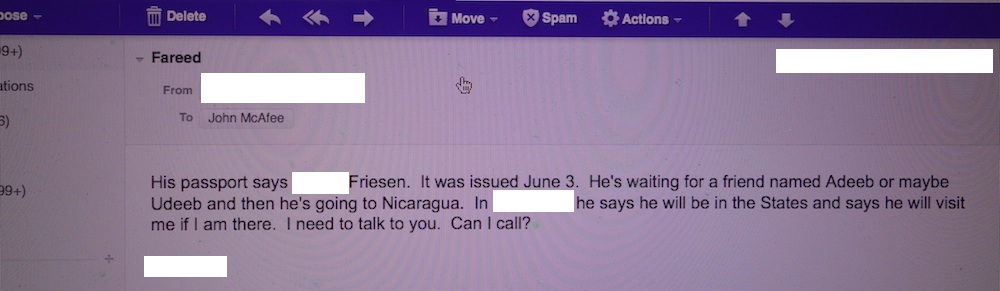
Her subsequent phone call was enlightening. We have disguised her voice:
Something was clearly happening that was not good. The following voice recording of a discussion with a well placed Belizean official details most aspects of the Iranian new identity process. We have disguised the person’s voice for obvious reasons:
Belize is clearly the central player in a larger network whose goal is to infiltrate the U.S. with individuals having links to terrorist organizations. What is different today from the wholesale Belizean passport selling of ten years ago, is that the false citizenships that are created for these men are coupled with a network of handlers designed to move the individuals, and their cargo, into the U.S.
The replacement resource that I sent to keep Farid company (someone capable of sidestepping Farid’s cruelty) emailed me many times concerning Farid’s vocal anger toward America. In one email she provided two crucialpieces of information that made things come into focus:
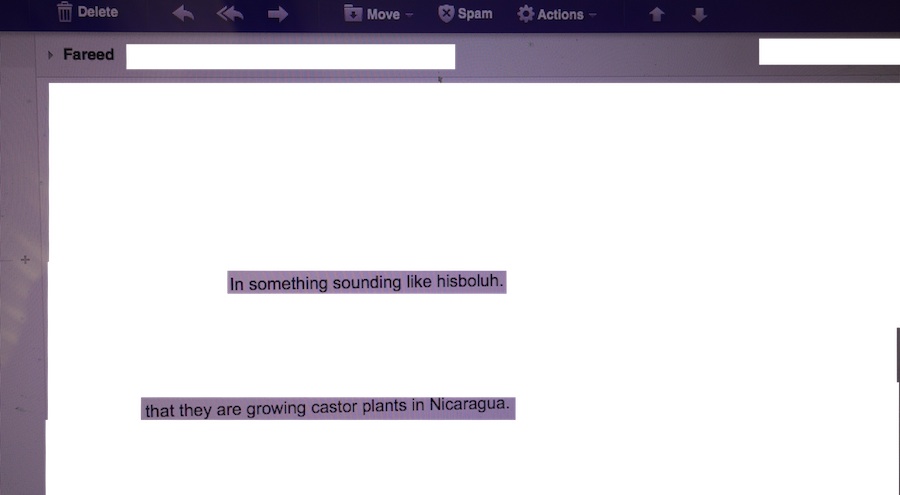
The Belizean official in the prior voice recording was either unaware of the Nicaraguan connection or, more likely, was afraid to divulge it. Here’s what the world seems to know so far:
There may be a Hezbollah camp in Nicaragua, but no-one seems to know what they are doing at the camp:
Hezbollah establish training base in Nicaragua
Hezbollah has created ties with the Mexican Drug Cartels – specifically the Zetas:
Hezbollah Hooks Up With Mexican Drug Cartels
Hezbollah’s Rising Profile In Mexico
Everyone seems to think that Hezbollah’s intent is to gain riches through additional drug trafficking. But drug trafficking is not Hezbollah’s intent, as the above reports imply. Hezbollah is using the Zeta drug transportation network to transport something similar, in weight and size, to the drugs that the Zetas know so well how to slip into the States. In return, Hezbollah is providing know-how to the Zetas in advanced weaponry.
The diplomatic world (the State Department) clearly knows that Belize is the architect of the current threat to America’s security:
Wikileaks from U.S. Embassy in Belize
Hezbollah terrorist with Belizean passports
but the State Department either does not understand the depth of the threat or for some bizarre reason does not want anyone to know the depth of the threat. In fact, they don’t even want people to know that Belize is sending terrorist into America at all. All official reports claim that the passports that people have been caught with are in fact forgeries and that the Government of Belize is not involved in creating false identities. Unfortunately, they are. And the threat is of an enormous magnitude. The substance being created in Nicaragua is being created by the ton.
I know all of this because I reassigned resources and for the past three months have had two people in Nicaragua that have made connections with the Hezbollah camp and I have three people in Mexico who have made connections with mid-level Zeta members. I will release no information at this point that will implicate these five people. Both the Hezbollah camp members and the Zeta organization, combined, have thousands of female connections. This small post will implicate no one.
Anyone who is truly interested in deeper process of what is happening can infer the truth from the information provided in this post. I have provided everything you need.
Belize is still a pirate haven. The stakes have just increased a few orders of magnitude. The current government represents a threat of enormous proportions.
My subsequent posts will expand on different aspects of the above as it becomes safe to do so. In the meantime, I am taking a well-earned vacation into the heartland of the Midwest. I blend well with the ranchers and cowboys that I lived amongst for so many years. They are a sympathetic lot.

180 responses to “A Clear And Present Danger”
Ransack Eclectic literature, and you’ll find no such disgraceful admissions.
Thank you.
I never knew about you as a person (and not the name of a software company) after hearing you on the Joe Rogan podcast.
Just wanted to send my regards from Amsterdam, The Netherlands. Hope you are alive and well somewhere. Even though it’s technically none of my business (as a non-us citizen), I’m still going to send your articles to the US embassy here, maybe it will get picked up.
Rusty. I do agree with you that the petition will most likely not make a difference white house level. And agree with allot of what you said though I’m.not going to point them out individually. I just think it’s better than doing nothing. Call it going down swinging. My thoughts are at the very least I hope this petition reaches enough signatures to require a response(though the response will probably e rubbish) and then the situation get just a bit more media attention and in the process educate a few more.people about the possible threat of a Ricin attack. As it is right now the majority of people has no clue what ricin is. If more people were.tuned in to the facts and dangers then if something did happen the people would be a little more prepared. There are steps that can be taken during a ricin attack that raises your chances of survival. But if there is no one that even knows what ricin.is or the symtoms then if something happened people would be clueless. Imagine the damage control if people in Hiroshima knew that after the nuke went off there would be a black rain you should NOT drink because it is VERY radioactive. If people had known they could of avoided the rain and the death count would of been dramatically less. I know we often take over the top measures that may result in pointlessness like possibly with this petition. But we have to do something. Often we feel compelled to help but have no idea how. Well this petition was just one man’s attempt at helping so as to not feel like his hands are tied. I encourage others that feel they cannot make a difference to at least try. Enough small attempts and eventually someone will hit the nail on the head.
No one is coming to take your guns.
.
The second amendment includes the term “well regulated” for a reason. If anything the Obama administration has made it easier for you to carry your guns.
.
But this blog is not the place for the racially charged accusations of the fringe element.
Wow it must be hard being you.
.
The Obama Regime? What about the Bush Jr. Regime? Didn’t they ignore the events leading up to 9-11 and take us into 2 very long and unneccessary wars?
.
If what John is putting forth is true, a petition will at least cause the Obama administration to say something about it.
.
We will let history decide if you and people who think like you are right about how Obama is some kind of Tyrant who wants to rule America. I’m thinking that clearer heads will be the ones who prevail on this.
.
David, those petitions do absolutely nothing. Do you really think a petition is going to make the obama regime suddenly stop and say “oh yes, we should close the border instead of keeping it wide open, and while were at it we wil give belize a call and tell them we changed our mind on sending us terrorists with fake passports.” No Dave, they don’t care what you think. They want to destroy America by any and every means possible and a little petition will make everyone feel like they have done something and someone will pay attention. Those petitions are for blind sheep.
The obama regime is purposely letting these terrorists inside the U.S. Meanwhile they want to gut the second amendment so you have no defense when these terror cells go active.
Many years ago Delmart Vreeland took his September 11 story to the world via the internet. Mr. McAfee has his story of human smuggling and drugs and their connection to US policy. US policy in the service of private interests who operate the Zetas. On the other hand, a Muslim Reconq
A private island maybe? You would of course, need security to keep the hooligans from infiltrating, lol.
https://petitions.whitehouse.gov/petition/investigate-possible-ricin-manufacture-belizean-officials-intent-use-against-united-states/0JVRTKS2
Please everyone sign this petition and share this link on every social website you use Facebook, Twitter Etc. This is the type of thing that needs to be going viral rather than a video of a dog carrying a cat back inside the house for the owner….though that was hilarious.
I was browsing Google Earth and thought Belize looked like a nice quiet place to retire, maybe explore some Mayan ruins. That got me digging deeper, which ultimately led me here. So disappointing… Is there any place on Earth where a person can just live and be without corrupt officials and hooligans fucking everything up?
Keep going John – I read the wired story and am fascinated. I want to know truth – feed us truth (and hopefully it will set you free?) 🙂
Agreed.
I continue to be surprised by media that pick up on this story and seem to not believe John’s description of his trojan horse laptop “gifts” and operation to infiltrate and gather information from the corrupt government of Belize.
After all of the extortion attempts, raids, property destruction and property stolen, of course (!) John would launch a counter attack using the “weapons” that he knows so well — spyware and social engineering to uncover the widespread corruption and dangerous connections brewing under the surface of the Belizean government and police force.
Case in point:
http://www.huffingtonpost.com/2013/01/07john-
McAfee-blog-Belize_n_2425516.HTML
I felt compelled to add a comment to the article as well.
Also, this latest video of the murders in Belize is definitely scary. That link should be sent out broadly so people can see first hand what is going on in Belize. As they say, a picture says a thousand words. – Z
Belize is so corrupt, such a shame. Drug dealer building major airport on Placencia peninsula. Ships to Mexico. Police are a gang.
1. After the April raid….I purchased 75 cheap laptop computers.
2. I next collected my human resources for the complex social engineering…Eight of the (23) women were so accomplished that they ended up living with me.
This sounds inconsistent with the rest of your stories.
I’m just hanging around on the edges of this thing, ever since I smelled the rat right from the beginning. You didn’t strike me as somebody stupid enough to randomly post about Bath Salts , and you may well have been running from corruption from day one, I reasoned. I followed your epic escape and would read about your escapes to my partner over breakfast and we would debate about whether you were loco or being painted as such. You played it straight out of a John Grisham book as far as I am concerned. It was epic. Of course, given your expertise, that’s exactly what you would do in that situation. What choice did you have? They were gonna get you and you outsmarted them. Holy shit!! I wish my kids didn’t live in San Jose right now, especially. I read the Google recipe for Ricin and I’m hoping the CIA agents who work for Google tracked everybody else who accessed it. You think?? Anyway, good show, matey. Besides the public service, it is a very interesting story and I always feel better when my instincts are right, don’t you?
The People on the street were filmed yelling and yelling at “GSU,” who look underfunded, and ramshackle. Eventually, after a couple bottles ae lobbed at the soldiers they open fire. not once but three flurries of shots. I did not see anyone hit but the film crew wasn;t focusing on the people at that time. Pnly the Shooters. Ugly Scene to say the least…
John…You were right about the GSU now classified as Central America’s newest Death Squad. Four people were killed Commando style with their throat slashed Colombian neck tie style.
http://www.youtube.com/watch?v=Zimr6rSWzYQ&feature=share
You can do this with Mac and Linux as well. That security cake is a lie..
Linux is by far the more secure OS however and MS the most vulnerable.
Will these be enough for you?
– http://fiwebelize.com/the-real-belize/
– http://fiwebelize.com/hon-gaspar-vega-no-apologies-for-giving-land-to-family/
– http://fiwebelize.com/more-land-issues-uncovered/
– http://fiwebelize.com/more-land-issues-uncovered/
– http://fiwebelize.com/cabinet-reshuffle-or-political-payback/ (this one happened to a UDP minister that spoke out about the UDP corruption)
– http://fiwebelize.com/the-belizeans-dream-lost-in-corruption/
In Belize, the govt officials will take anything this is of value and free. I work in the IT field and can say that bots take no time to get installed and configured, in fact you can mass set these up.
I wish he would have gotten one of those laptops to Dean himself.
John,
Have you seen the latest in Belize?
http://vimeo.com/57044512
I too saw Alex Jones on Pierce Morgan.
He really came off as a Raving, ranting, finger pointing , yelling, threatening, Bonkers Bafoon… and Bully
It made me question McAfee’s choice of granting him such an important interview, but what do I know?
Maybe? its because of Alex Jones’ 1 million listeners?
Maybe it was because Mcafee was given 15 minutes of fame and airtime to tell his story in complete sentences rather than main stream media style of “sensational sound bites”
Maybe Alex Jones built in audiences are more likely to believe the unbelievable with their total destruction by ” globalists ” mind set
I think Mcafee gave “good show.”
cool, calm, concise, clear and in control … a much more affective communication style than Alex Jones tyrannical meltdown.
I think we should have learned by now, not to try to second guess Mr. McAfee’s choices about anything in his Life.
Remember, it is He, not Us who is writing the script of his life as he knows it.
He said in a recent interview that his whole life has been Mystery… even to Him .
How could we possibly know what is best for him ?
As we have witnessed, Mcfee’s life keeps changing in vibrant chaos , nothing is a constant …or “as it Appears to Be” .
As for myself, I’m in for the full ride, trusting the story will unfold in its own time… it takes as long as it takes. He’s “Just setting the table” the main course has yet to be served…As with any good story….its all in the timing .
Not odd at all. That no one has come forward for the reward. Even dishonest people. Tells One and All that it is almost Positive that the GOB is either complicit in the Murder, or aware of Who is. I have been reading the news websites from BZ, and there has been NO mention of the investigation or any results. Laughable but not funny.
To simutaneously claim that JM is NOT a Suspect but wanted for questioning only – AND to NOT appear to be investigating the Faull Murder – makes the GOB look so Sadly Complicit. These People are Either Not Too Swift Mentally or They Simply Do not Care about World opinion. That’s foolish. They will surely go down with sich Impudence..
Anyone can read the news from Belize online. Even though official corruption is rarely “Copped to,” haha, in the ‘press,’ One can easily see that Society is run by Crime Lords. Official and otherwise.
According to John he started this after the raid in April. That would be 6 months of ‘spy’ gathering, software installing, and data collection before Mr. Faull was murdered. What was your question again?
WTF??? That’s an International Airport? Looks more like an open invitation for criminal activities. SMH….
You ever heard of Goggle??
It’s extracted from the castor bean pant and is considered the second most lethal compound in the world …. the first being plutonium.
I was traveling in Belize in 2010 and although the Cayes are amazingly beautiful and peaceful, the mainland seamed incredibly sketchy. I remember waiting in line with tourists to exchange some currency from this guys, who turned out to have a gun besides him. Also, it seems people fear the police as if they were not really there to protect them. It also seams that one of the luggage boys in the bus pickpocket me while I was sleeping. Ahhhh. Belize.
“‘I purchased 75 cheap laptop computers and, with trusted help, installed invisible keystroke logging software on all of them… began giving these away as presents to select people…”
Want your life to be spied on in the same way? Let me add the key word that John left out:
“‘I purchased 75 cheap Microsoft Windows laptop computers and, with trusted help, installed invisible Microsoft Windows-based keystroke logging software on all of them… began giving these away as presents to select Microsoft Windows-using people…”
There are three flowers in a vase. The third flower is red.
Waspam International Airport: http://www.flickr.com/photos/ashawls/5696672050/ => http://maps.google.com/maps?q=Waspam+Airport,+Nicaragua
What’s needed is the receipts for 75 computers.
Shouldn’t be to hard to come up with.
I wonder how many people posting on this blog are for real and how many are T R O L L S!!!!! Trolls go away and find someone else who wants to listen to your rants.
Look, I’ve been reading this since it began… Sincerely, doesn’t it look a bit… unrealistic? I hired 30 people (didn’t that take some time?… a few weeks at least?). I installed some software on the PCs. What software? Didn’t that take some time? (a few weeks at least?) I convinced the goverment to take them (Didn’t that take some time, at least?)
lmfao…. ‘gang style hit, one bullet to the head, no mess or blood other than on the victim.’
Yup, that was definitely done by someone in a “drug fueled rampage”
Thanks for the laugh.
No, I don’t find it odd….I’m not surprised at all. For someone to collect the 25K, they would need concrete evidence against the murderer. You make it sound like poor people automatically become liars if enough money is flashed around. It was a pretty clean hit from the sounds of it, which would lead me to surmise that anyone with knowledge has intimate knowledge…. not likely to confess. Speaking of clean hit, do you really think someone on drugs could have pulled that off? Especially the MDPV that you (expats) are convinced John was making and taking. From everything I’ve read, that kind of drug doesn’t make you the most stealthy individual…which you would need to be to pull off the execution style hit. But, you can’t have it both ways.
Nope. Which translates to they don’t know or they don’t care who really killed Greg Faull. By not releasing any information about their ‘investigation’, it allows the “wanted for questioning” aspect to fester among the masses of the idiot population. I see that lack of information as just another atrocity they have perpetrated against John, and most assuredly against the Faull family.
Obvious question; why would the Mex cartels trans-ship poison North and try to wipe out their biggest customer.?
Answer; they ship poison that kills their customers anyway and in this case they get paid up front, so it is six of one, half a dozen of another.
I love all the fake comments on here John. Well done, but no one really believes all this bullshit. Everything you’ve done up until you “escaped” from belize is a lie or distraction from the real truth. That you killed your neighbor in a drug-fueled rampage, the result of a long life of drug addiction, god only knows what sort of psychosis you’ve been in after freebasing bath salts for 3 years.
Can’t wait to watch the movie about this one..
KEEP UP THE GREAT WORK. I love the updates with Alex Jones, you appear to be onto something very significant and must look after yourself. Don’t hold back information that could put in danger, make sure you get it out through the alternative media.
Hey bud,
You’re on Ars Technica and Hacker News:
http://arstechnica.com/tech-policy/2013/01/the-bizarre-tale-of-john-mcafee-spymaster/
http://news.ycombinator.com/item?id=5018052
You need to step your PR game up, the general attitude is that you’re crazy/schizophrenic. I would recommend hiring a professional to help with that. If you can get testimonials from other people on the corruption in Belize, it will probably help too.
We’re rooting for you. Good luck.
bahahahahaha
Politics is the game, every game have rules. Politicians have their personal interests, they get salary and have to keep their positions. McAfee does not belong there, he doesn’t play according to their rules because he doesn’t need/ collect the salary… His appearance is unpredictable for all, like a third King on a chess board. They will try to ignore him. They want rule the world no matter where it goes, up or down.
Also, I do not think anyone will chase McAfee to hurt him for disclosure his foundings. It happened and this is it. Now those people have to deal with the consequences, not with McAfee. McAfee came to Belize not to fight corruption there and not to look for Hezbollah. He is a stranger in that world, they understand it. I am sure they are amazed and admire him too for his abilities to do things. Additionally, I am sure no one gov now would want to get close to McAfee, because everybody have something to hide. This already sounds/getting entertaining:).
Relax, John, no one will kill or hurt you. Only crazy can do it. You are a living legend and now you are in your birth country. But still better to keep people and guns around. Belize now have to deal with their own problems, so the gov.
John stated he is libertarian, but that he is not politically motivated or inclined.
.
If he wanted to run for office, he could have done so in Belize…yes?
.
John has already sold the story rights to his life.. So no payday for you…
mmmkay…
So we have heard the Illuminati theory, and this ultra anti-semitic theory. The internet can be a scary place indded.
.
And people think John is crazy and on drugs…
Finally heard the interview, I cannot believe our government does not take this more seriously. What is happening with Sam?
I agree with WEB. Please let us know you are ok.
Joshua Davis did the eBook, Jeff Wise is the obsessive one. Just for clarity.
.
Don’t you find it strange that John is only wanted for questioning, yet they refuse to just question him over Skype or let him do an affidavit here in the States?
.
Do you honestly believe that someone on Bath Salts could succeed in pulling off a calculating execution style murder of a man who didn’t really know him and is much larger than him?
.
I don’t find it odd at all if the murderer of Mr. Faull was say, someone in the government or someone in a gang. It may be difficult to comprehend but money is not the highest motivator in a country like Belize.
.
I am not naive, if John murdered someone, he should go to jail. I honestly believe that having to put down his own dogs was difficult for him. You notice that when he talks about the April raid he always mentions how they shot his dog. This was a traumatic event for him. It would be for any of us.
.
I’m keeping an open mind to see what unfolds…
https://www.whoismcafee.com/a-clear-and-present-danger/john2/
The parking lot of the Super-8 in Flagstaff AZ?
Midwest: A Great Place to be.Some People have Minimum Requirements of Integrity and Honor. High Minimums. There are such places on Terra where it is the norm rather than the exception.
One thing about the Third World. Well two things.. It’s Great to be a Novelty as a resident.
AND it;s NOT great to be a novelty.
Low-Key isn;t enough in some places. Just a matter of time. One Stands out. Someone is going to decide to do something stupid at some point.
Ahhh, The Sublime Circle of Life… Anyone who wants the Job Should be Disallowed from Performing It. (Police and Politicians).
I started collecting data in May. I am still going through it
“Real” Lives.. ? That’s a laugh. If I surfed everyday for the rest of my life, I would be the luckiest Individual on Earth, or the next Habitable Planet.
Two reasons: Someone adores attention. OR someone ACTUALLY cares about others. Regardless of Balances in a Bank. I would go with the Latter in the case of JM. I know that there is no small amount of Womanizing also in that mix. JM is one of those people I can identify with. Uncategorizable. No Limit People. Has nothing to do with the Bank Account. It is about Life Choices.
I believe that John has previously stated (somewhere on this blog) that he is a Libertarian.
yo im a coffee fan, got any recomendations? i just had some jamacia blue mountain and kona….i hear u guys on the west coast get the best coffee in US..
ive read quite a bit on john myself and well aware of the bath salt thing and jeff wise ebook etc….but it seems hard for me to believe that john put together a professional intelligence gathering organization of over 30 people and then went through that extremly massive amount of data in something like a months time. and in that time his neighbor died and the guy next door who coincidently employs murders and thugs aka the people who do drugs, was a few houses down from the murder scence the night of the murder….and he just happened to have pictures of himself with shotguns and armed thugs while getting raided for drugs and guns. again this is coincidence. look im not saying anything other then that its important to be objective and look at the big picture. the simplest answer is useually the correct one. dont you find it odd that in a country like belize, thats so corrupt and poor, not one person has volenteered or forcefully came forward to get johns 25,000 dollar reward for the murderer of mr.faull?
So maybe I’ve missed it but any luck on finding, proving Mr. Faul’s murderer?
There is no way $100 billion worth of coke gets into the heartland without government sanction. There is no way a network of poisonous agent manufacturers sits on a cache consisting of many tons of chemical, having the same ease of access as is available to the coke lords, and then never uses it (especially if 1200 of their operatives have been planted here). Hence, I find the theory put forth here is a non sequitor, unless the chemical is mind-control drug.
I lived in Belize for a year back in the early 90’s. I guess it’s not the same anymore. San Ignacio was a wonderful little town. I miss it.
The reason the US government is doing nothing to stop this is because the shadow government wants 95% of th world population eliminated.
The shadow government is the Rothschild Mafia who created, own and control Israel and the Federal Reserve both of which they are using to destroy America. They control nearly all media but the internet which they will soon censor or shut down.
The bigger goal they are going for is depopulation while they are in their luxury underground bases which they have spent over $40 trillion building while bankrupting the USA. God’s chosen will hide in these underground bases which are the command centers over the slaughter of humanity.
They have nearly achieved their goal and are in the final stages to create a world only for “god’s chosen” who are the zionist criminals and their unarmed defenseless goyim slaves who will live in total poverty. The search for food will keep them from rising up and easily controlled by their high tech police state drones and robots.
Yes I agree with others about infowars. Good source to get your voice out for one event but I would avoid it in the future. Part of your plan is to get knowledge of yourself out there. Get the tough questions asked so you can answer them to make sure people know your not a mad man like people have made you out to be. But attach yourself to a gun crazy screaming lunatic already thought to be paranoid and a manipulator of information(not my view but view of many) will be counter productive beyond what you have already done on his show. You were making progress informing people of the truths that need to be known and to shed a better light on who is john McAfee. I suggest future attempts to reach out be made through someone in between the mad men of CNN and the mad man Alex jones. I love Alex jones and think he hits the hard topics people are afraid to talk about and he is a soldier of freedom. But Alex makes his living and thrives on being seen as a raving mad man and at this point you might not be able to afford such accusations. I feel foolish making suggestions to a tactical genius but I think this one was one of your only bad calls. But how many times have we found out something questionable you have done has turned out to be a brilliant angle all apart of your genius plan. I would ask you “So whats the next step? What next in johns plan?” But I wouldn’t really want that answered here in the blog anyways. Anyways,If your ever in the memphs areas and you need any help no matter how big or small I’m here for you. You take care of yourself and enjoy yourself. I know you feel this all is the best thing thats has ever happened to you. Gives you soemething to work on and allows you to flex your muscles and keeps your mind busy at the same time. I know it feels good and satisfying. Grats on all of this. Enjoy your Buffet. Racing Genius minds need food also. God Speed Brotha.
Valid comment, WEB. I was Not aware of these specific reports prior but I dont typically read such news. However, most U.S. citizens are aware of terrorist sponsored activities in Latin America or, such news should come as NO surprise. But, in the U.S. we have very short, selective memories and short attention spans so, knowledge and perspective are catch-as-catch-can. My question stands and we’ll see. To all good ends. -S
I agree with someone’s comment: “…just be very careful not to join someone else’s political cause in the process. If you do, you will lose what credibility you have built with the public”. He probably meant InfoWars. There are a lot of nice guys and political views there but all of them are far from perfect, so better not to take their old “sins” onto your newcomer’s shoulders. You are more popular and stronger than they are, any way. It is better to keep independence and top level of individuality. It will pay.
Why mainstream media does not cover this… My feeling is:
– John is a person who cannot be controlled, but media likes to be in control;
– He is too powerful in his brained activities (or even practical jokes), they feel confused;
– all what he did, if it is real (however it is believable, we already know anti-virus McAfee brand), make him a super-duper / superman of our times and of such level, not many saw before.
His activity shows how useless other people are (including mainstream media) who suppose to do the good work but they do not…
By the way he performed the magic from “normal” people point of view, I believe he is rh-, he is much above.
All I said here is a simple realty.
You didn’t have to go to so much trouble. There’s a little program called mobistealth that would have done all that for you. And in closing I would say what you’ve obviously already figured out: the best defense is a good offense. Nice work.
Well, if thats true, I make some damn good coffee.
So if he ever wants to have coffee with some idiot on the west coast, I am that idiot.
AH! SHUT MY MOUTH AND MAKE ME DRINK SWEET TEA.
thank you
Hey John, how’s the R & R going? Is there any way you could post a little more often? It seems that with every comment acknowledging the plausibility of your information comes an ever growing amount of concern for your safety. An earlier post also questions Chads safety. Maybe a ‘hey y’all’ from both of you would be good. 🙂
I saw an excerpt of a new Navy commercial that is soon to be released on the effects of taking bath salts. The news caster speculated that the Navy is concerned with its use within its ranks. Very scary stuff. Didn’t even remind me remotely of JM.
John’s confession of hacking the Belize government makes a lot of sense. It explains the scale and relentlessness of their vendetta, and why to run was his only real choice.
He deployed an impressive investigative network and dug up fascinating stuff. Yet, I find it inconceivable that his resources could compare in scale to a real intelligence agency’s, or uncover something they did not already know, least of all when it comes to large-scale importation of Islamic terror.
So, is Hezbollah really working with Zetas to smuggle Nicaragua-made ricin to US operatives? Well, Google’s news index says the mainstream media has not picked up on this story at all, now after more than 2 days. It is the same MSM that did not mind reporting his every sneeze, including quite a bit of hearsay, while he was on the run. What does this suggest? That the MSM’s global self-censorship mechanism was activated in this case. This only happens with stories deemed sensitive, never stories about people making claims that are outrageously false. So, in my eyes, the MSM’s silence has given the Hezbollah-Nicaragua-ricin connection some credibility, although the truth is probably more complicated.
But, even if somewhat true, where does this leave John? Let’s see… Hezbollah is unhappy; he blew their cover; they will have to relocate the ricin plant, rebuilding the supply and distribution chains; costly stuff. CIA, who have probably been watching the Nicaragua operation under the microscope for years, must be raving mad, as he just spooked a major target. Belize? The spotlight of scrutiny has not yet hit their lucrative little enterprise, but it’s likely a matter of time. The best way for them to retain it now is to find a way to publicly discredit John. Charging him with computer crime (based on this post) is a plausible avenue of damage control for them (I don’t see them being stupid enough to file an extradition request, though; it’s not worth the unwanted publicity of a protracted appeal process).
So, you’ve got Hezbollah, CIA and Belize. That’s quite a stupendous alliance of powerful enemies, John, and a confused, bemused, and distractible public, as your only useful friend. You are emulating Peter Pumpkinhead here; you should be aware of how these things end. I suppose you have no fears about your own life and liberty, and all you care about is “hope for humanity”, so, fine, go for it, we won’t stop you. Just be very careful not to join someone else’s political cause in the process. If you do, you will lose what credibility you have built with the public.
“He is known as a practical joker; Why would mainstream media take a chance that they might publish something as threatening as this and it not be real”
Why would they NOT take the chance. I think if you do further investigative work of how the media has changed since the 80’s, you’ll see most media news outlets were merged into the entertainment divisions by their parent corporations. This means sensational and partisan news is needed to run a profit. The news used to be run, at least in the States, as a quasi-public service. Today, it is filled with nonsense. When you talk about what should be done and so forth… well the job of the news is supposed to be to report the news. A job they have not done too well exactly when it comes to foreign affairs, and likely for partisan reasons. As for the bath salts and John McAfee being crazy… this is almost entirely a media invention. He escaped Belize unharmed when they killed his neighbor, all his dogs, destroyed half a million dollars worth of property, and detained him illegally for hours. Then they used his friends as leverage until the press hit the story… So the narrative was created by the press. If they don’t follow this story its because it goes against their own narrative. The reality is that despite what the McAfee anti-virus business did with his original software, John McAfee is still an IT security expert on a semi-genial level. Or at least he was back in the 80’s. Installing keyloggers is not that hard, but getting them to 200 people in a government enterprise environment kinda is. I don’t see why anyone would doubt this story unless the media is too corrupt to cover it. They have to follow the “John McAfee is crazy” narrative, until the evidence is so overwhelming, he is vindicated. Well, if there is a ricin attack int he USA (God Forbid), guess who is going to be getting a phone call. At least he went straight with the information with whoever would hear it. I think like a lot of other free thinkers and people chastized in the public, he will be vindicated with time. Besides, McAfee has sort of identified himself as a “retiree with nothing to lose”, “living in the moment” sort of guy. I don’t see how this could be a joke at all.
Just wondering how many of the “already known” stories you were aware of before the links were provided? I can’t recall seeing any of them before, but must admit I watch a limited amount of American based news. Perhaps this is a revelation for more than just me?
scha·den·freu·de noun, often capitalized ˈshä-dən-ˌfrȯi-də
Definition of SCHADENFREUDE
: enjoyment obtained from the troubles of others
Always have and will be a brilliant man!! Amazing!
If forthcoming info will be detrimental in some way to corrupt Belize officials and/or, less doubtful, Zeta cartel members (like they care), Hezbollah/terrorist cell operations, or any other malicious operators who might be exposed, then John would be in increasing physical danger from someone possibly trying to shut him up (just like in BZ in Nov) right? He admitted as much in the interview last night and remains incognito, right? I think these organizations could find him fairly quickly if they wanted to. And one (obvious) method would be visiting Chad. Chad, you could not have anticipated this scenario, now involving accusations and insinuations at a wider array of dangerous criminals a little closer to home. That’s John’s trip. How about you, not to mention the others, but you feel secure and confident with continued involvement in this?
The comment about him being a saint was meant to be snarky I think.
.
I don’t kiss anyone’s ass. I believe that John is manipulative, but not in a mean spirited way. I think his practical jokes are meant to amuse himself. I have honestly never read anything about John that would suggest he is mean spirited at all. In fact, many people have commented on his generosity.
.
The whole bath salts thing stemmed from Jeff Wise knwing that John used the stuffmonger moniker and he dug it up. Jeff Wise has some kind of weird obsession with John from back in his aerotrekking days.
.
Truthiness and Facts matter.
Meditation and yoga really helps to calm the mind. Try it. Hell, buy John’s (yoga) book!
If he wants to make a Positive difference, he’s chosen a suspect way of doing so. What difference is this already-known information going to make, Connie?
John McAfee is now has more girls than Hugh Heffner.
my statement landed in the wrong spot, sorry. It should be under Robert Gemerek.
Are you able to move it, Chad? thanks
Exactly Connie, he could have just left it alone once he was safe.
There is no need for ” a diversion ” as some have called this. JM is NOT wanted, and does not need to divert anyone’s attention AWAY from him. I am amazed at how stupid people can be. The same baseless arguments keep being used by some, and enough is enough!!
Any bullshit we were fed along the way was a necessary tactic, and nothing different than our own Government does. It’s called survival people…..and it was JM who told us about the lies.
He has stated many times he did not kill GF, so stop saying he hasn’t. And while we’re on the subject of murder, WHO really believes a messed up, high on bath salts individual could actually sneak up on someone and then with precise accuracy land a bullet in the back of their head? Then escape without leaving a trace of DNA, or getting anything on themselves. WHO? Have you ever seen someone who’s really high? They’re not the most graceful or coordinated individuals.
Don’t you haters…names are above and throughout blog…think it’s time to cut your losses? You have no credibility if all you do is scream about things that have long since been concluded. Your statements sound shallow and idiotic. Could you possibly add something interesting and concrete to the conversation instead of the same old shit?
I believe there are probably many reasons for the main stream media to not be involved in this. Of course these are just my take on it. When John was on the run, every news organization wanted a story on him. If he sneezed they reported it. It was a human interest story. Murder and mayhem. A rich guy literally being hunted like an animal. Check. Now, I believe that its kinda like the boy who cried wolf. I don’t want to get into the bath salt saga, but even Alex Jones brought that up. He is known as a practical joker. Why would mainstream media take a chance that they might publish something as threatening as this and it not be real. Also, I think that for them, there needs to be more data (which I know is forthcoming). For those of us following this blog since inception, most of us believe John is telling the truth on Hezbolah. Yes, he has given some misleading information when he was on the run to protect his life. What smart person wouldn’t have done this? John doesn’t seem like what Alex Jones said, “the greatest actor” and would given errant facts on what is going on in Belize and Hezbolah. He didn’t have to say anything once he was back in the states. He could’ve just faded into the sunset. He didn’t owe anyone any of this. He has given this information freely, I believe, because he wants to make a difference in this world.
He didn’t sell any laptops. He gave them away to the greedy Belizeans who were all to happy to take them.
this entire thing has the air of a really lame practical joke. and wow its just kinda sad to read things like people calling you “john the saint” and kissing your ass. you sounded like you were reading off talking points at the end of that alex jones interview, you repeated yourself multiple times but whatever man im gonna go snort some ricin and say you told me to do it. then im going to spread a rumor that you carry a tiny vile of ricin on your person at all times in case things get out of control.
Now I know how Abu Nazir got in 😀
On a serious note, why hasn’t this been investigated/covered by the main stream media?
Great work John, you deserve to be commended
I have been hoping that Internet publicity would force private negotiations resulting in a solution acceptable to John. But if all information now made public is insufficient, then other efforts should be made.
I suggest that written complaints about John’s being threatened, to cover-up corruption/illegal activities which caused him to leave Belize for personal safety (to save his life), be sent in letters directed to US Senators & Congressmen. Also information on the “Claer And Present Danger”, to USA National Security from Belize, can be included in written communications.
To assure response, requests should be made to Senators & Congressmen, for selected representative(s) of John to have a personal appointment scheduled to be held in Belize US Embassy. The following Consular Officers are requested to attend meetings at US Embasy in Belize.
Belize Ambassador Vinai K. Thummalapally
Belize Deputy Chief of Mission Margaret Hawthome
Chief, U.S. Military Liaison Office LTC/US Army Darren Lynn.
American Citizen Services (ACS) Counsular Section of US Embassy Consul Ms. Arleen Grace R. Genuino
Bereau of Western Hemisphere Affairs Assistant Secretary of State Roberta Jacobson
John McAfee attends meeting by video internet conferencing
Personal Repersentative(s) John designates attend meeting
————————————————————
Serious issues could be taken back to the “origin of problem”, which are all in Belize. Problems have been assisted to develope by inaction and/or complicity, in US State Department diplomatic relations, with Belizean Authorities. This is the responsibility of US Embassy in Belize, and it is time for them resolve problems that they enabled.
Smart Move says that John should take an offensive directly to the US Embassy in Belize, by encouraging US Citizens to be there on-site and demand that USA, Belize, and International Laws be enforced. And it is time to petition the US Embassy, to formally request that US Justice Department initiate a special investigation, with the objective to properly enforce the FCPA Federal Corruption Prevention Act.
John needs repersentatives to personally go to Belize and demand action at the US Embassy, to enforce law to protect all legal rights of John (including John’s foreign investment which was encouraged by US Government Policy). Smart Move volunteers to go to Belize (at his own expense) on this mission with any other repersentatives John may designate. Anybody else intrested in putting their time & money where their mount is?—to end this blatant international corruption, and help protect the USA from a “Clear And Present Danger”.
I suggest this offensive move, but only if John would approve some US Citizens going to Belize to politely but firmly demand action at the USA Embassy. Interesting to see how corrupt Belize Authorities would react to such a legal petition made in their territory?
If I go, then I can assure that the US Embassy will react with some quick actions. I cannot predict unintended consequences because there is obviously much international intrigue involved, but there will be “transparency” resulting from such a visit to US Embassy, and Consular Officers will be forced to respond to the issues involved.
To assure that our Senators & Congressmen respond and arrange meetings John may desire, letters to our Congressional Repersentatives need to be crafted, which makes them clearly responsible for any future biological attack against USA, if there is inaction in this matter.
John’s interview in InfoWars nicely tied all previous posts togeather, and the relevant issues are very clear now. Belize Corruption has increased to the point where criminally corrupt Belizean Authorities are an imitate danger to us all. I am available to assist John as he directs. I suggest a concentrated communication campaign aimed at US Senators & Congressmen, but nothing should be done without John’s directions as he is “Captain” of this blog, who sets course and timetable to successfully complete his story.
John the Saint… He is innocent of everything and we should take his word for it that he is a victim in all this. So sad…. So sad!
Hi, John. Was just wondering if you still have the money from the AntiVirus company, if your wealth is something the gov’t over there is eager to get their hands on?
Now am worried about your anti-virus, is it as malicious as you? Will you get tried for selling trojaned laptops to unsuspecting people and invading their privacy and stealing their logins? In the UK, you’d go to jail for that. How about a Nicaraguan jail? Will you go back and face your crimes? To me all this reads as crime, crime, crime!
I’ll be disapppointed if McAfee doesnt star in the next Mission Impossible or Iron-Man.
Be safe John, we are more worried than ever that you remain a target of far worse players than we imagined.
John McAfee for President . Who cares all theirs foolish step-by-step politicians’ rules. The US had/has all: ex-alcoholic W Bush, bullshitter with phony papers black one. It is time to get someone with highest IQ, who protects the country not for money. I believe/hope John is Republican. Actually, what you John did, no one else could. This is fantastic.. This post explains everything. Publish quickly all this in your book. With big publishers it would take a year or so. Do it yourself, or email me, I have a small publishing co and can help you to do it within 3-4 weeks.
I believe you John. I hope your struggle produces the downfall of the guilty! God bless!
Here is the interview: http://www.youtube.com/watch?v=xsndNiCasw8 starts at 48:40
Well done. Ever thought of going on Michael Savage radio? His show is often about borders.
This would be my question: Did the powers at be learn about your computer taping? And if so, when? Does it coincide in and around the time of the killing of your neighbor?
Nothing on rss feed
Has john been shut up?
Was Alex Jones another smoke n mirrors?
As crazy as the story is, following along it does seem believable. You may have just thwarted our govt’s next false flag. I’m willing to bet our friendly local government thugs are on the border shooing these terrorists in and delivering the ricin to their hiding places personally. It sure wouldn’t surprise me one bit the way our thug intelligence services behaves. You didn’t just get back at the Beliz governemnt, you kicked our corrupt government right in the balls. Hats off to you. Please stay safe. You can see the Zetas execute “snitches” on bestgore.com, don’t let your guard down. If you start letting your guard down, go to that site and watch them cut off someones head with a chainsaw and that will get your motivation back. For the rest of us, we should prepare and educate ourselves on chemical weapon survival at home and keep our family safe. This would be the best way to honor McAfee’s sacrifice. I will. Thank you for the warning and sorry for your loses. Being rich doesn’t make it any less troublesome.
Compelling information. You have a great ability for protecting yourself and discovering the truth. The public must hear about the high levels of corruption that is occurring everywhere. It is wonderful to have you writing for the blog again. I like your writing style. You are looking good. Hope you are well. I am sure we would all love an update on Sam. Please? I hope the mid-west treats you good.
Heather
Some of us posters will offer advice on things we know or to be helpful.
.
John is a big boy, he can do as he pleases. I believe in personal freedom. John has always lived his life the way he wanted to. On his terms, by his rules.
.
My only wish for that would be to hope our paths cross some day. John McAfee has been added to my list of People I would like to meet.
.
I don’t do drugs and rarely drink, only occasionally wine, so we could do coffee. I respect that he is so serious about his sobriety and I believe he is still clean and sober.
@Anwar, I too have been worried for John’s safety given this current release of information. The CIA has funded covert operations in Third World Countries for decades, and I agree with you that they must know something about the activities in Nicaragua. But then again, I hope not if indeed chemical or biological weapons are being produced. The CIA’s involvement in these countries is primarily to retain power, control and economic gain for the USA. Imagining they are aware of this and do nothing about it is even scarier. Hezbollah and the MM are indeed bad mofo’s, and we would be stupid to imagine they haven’t any operatives in America. As for John, I recall near the birth of this blog many suggested he just “get out of there and disappear” for his own safety. 7 weeks later and he still hasn’t given up….and I don’t think he will.
Hold on to that Luck ‘o the Irish JM.
Mr McAfee, I thought I’ll leave another comment.
What you are doing is very brave and although I would advise you to stop, let it all go and devote quality time with your family – there is a big part of me which actually thinks that you have earnt the right to call it quits when you feel justice has been served.
It takes a Messiah type character to fight this corruption on earth and I honestly believe that you have all the qualities.
All the best!
Some people are above the law and when we have a situation like this we will never have justice. That is why I am so anti establishment and the main stream media.
I take my hat off to John McAfree for treading on an area where even the bravest of us will refuse to tread on. That takes some courage and balls and as much as I like John’s indefatigablity as I do George Galloway MPs. I think the saftey and security of John McAfee and his family should come first.
Whatever John does from here on he has my total support.
Mr McAfee, You have a valid reason to be pissed off at people and I support your cause, I think it’s only right that you get the justice you deserve.
The world we live in is full of double standards and hypocrisy from hell. I am sure the CIA are fully aware of what is going on in South America if not active in supporting some elements you consider as unsavoury.
Stepping on Hezbollah and the Mexican Mafias toes is a step too far, their reach has no bounds, things could turn very nasty from here.
I am shocked that none of the other posters are advising you to let it all go now. This is a time to enjoy your money and the company of your family.
Those you consider your best friends today will stab you in the back and sell you to your enemies if the money is right. There is no such thing as friends Mr McAfee, the only friends you have is your family.
I wish you the best!
“but the State Department either does not understand the depth of the threat or for some bizarre reason does not want anyone to know the depth of the threat. In fact, they don’t even want people to know that Belize is sending terrorist into America at all.”
—————-
JM:
What are some possible reasons they wouldn’t want anyone to know about the threat (understanding it would be speculation by you, albeit informed presumably.)
Is it possible they want another disaster to happen to justify to the public new advanced surveillance technologies being rolled out.
You’re loved and respected the world over sir – please keep up the intel and look after yourself
Clearly not the makings of a lunatic. Impressive. Im taking notes.
The honey trap snaps shut!
– Fake Passports
– Hezbollah
– Ricin
You should write a movie script.
You’re still in the dark.
Welcome to my team!
Wow. Really do stay hidden John, this is much more than we knew intellectually, but many of us sensed great danger and that you needed to leave. Now we know the more and yes we were right and you were right in running. As far as Johns personal life, God has a habit that the elite always hate, in using people that have a past to greatly expose corruption and bring great change in other ways. Not many noble, etc. But oh nobility shines through here, John. Thankyou from one who knows how bad this world is getting and how few will speak the truth, and how many sleep, THANKYOU!
is that the Cracker Barrel in Springfield?.. I live in America’s heartland and ever since I learned that John was a peddler in his younger days I feel akin to him it’s what I currently do
barrow did, replace a band of thieves…the musa crew..!!
Sandwillow Are you kidding me with mainstream media ? take your computing device and search on the internet machine using the google aparatus and count how many if any mainstream outlet has reported any of this today …
But… a few weeks ago within minutes they were all reporting that John purchased new shirts in south beach .
Why does the dog wag its tail?
Because the dog is smarter than the tail. If the tail were smarter, it would wag the dog.
To much bad shit goes on behind closed doors
John your just the man to infiltrate it
Keep your head close to the ground
Good luck
“Biological weapons experts estimate that 8 metric tons [of aerosolized Ricin] would be required to cover a 100 km squared area with enough toxin to kill 50% of the people.” Even one ton in a subway line could be absolutely devastating.
check out the press on: http://betabeat.com I think this site doesn’t allow cut and pasted articles. so I can’t post the entire article, but it’s on there (as posted today).
Crazy information in your post – we are living in a crazy time post 9/11 — living in any foreign paradise comes with a great price. I am sincerely sorry about the loss of your dogs and that you are not with Sam right now. I hope she is safe and in a protected status.
Your home in Belize looked to be in a tropical quiet paradise location, I am very sorry that (it seems) you will never be able to return.
One of the most important lessons I have learned from living in third world countries for a good part of my life is to be as low key as possible, not be seen too much, let nobody know your business or your monetary status. And to get to understand your local community, and the good hearted people who have practically nothing.
Amazing stuff John. Be safe.
And it begins. I have learnt so much from this blog, and surveying this since day. I hope this can shed some light to those in the dark. All the support from Canada John. Once again I wish you, and the ones you love love, respect, and peace. Till the let the heads roll, and leave every stone unturned. To seek, strive, not not to yeld!
Over the top scarey stuff, but highly probable, given the corruption of those in power. It takes a brave man to implement a plan to expose it to the world. Bravo John, and Happy New Year. May you receive deserved respect for attempting bring justice back to Belize.
JM deliveres Flying scissor kick to the head of Barrow knocking him directly to the ground!
Lead, eat, sleep and bob & weave!
Best,
GJ
John does not drink or use any drugs beyond cigarettes and coffee, but I’m sure the sentiment is appreciated.
Good work Captain.
Well let’s hope the U.S. gov. already knows about this and is taking it more seriously than they did evidence 9/11 was coming.
Random points:
-Legalizing marijuana would be a blow to the Zetas because the markets for other drugs are much smaller. All over the world the drug/mafia/ money laundering/ terrorism networks are getting stronger.
-It’s important all you folks reading this don’t fall for Palestinian propaganda that whips up hatred at the U.S./Israelis and makes Latin America more penetrable for terrorist groups.
John if you ever find yourself in the SW Missouri part of the Midwest I’d like to buy you a beer.
good job John, keep up the good work and intel!!!!
damn dean barrow just got pwnd. this is great, get those fuckers.
Call T. The fixer
Roll Tide
LMAO.
I’m happy you feel good – you should.
And seeing someone stand up to stuff like this on such a massive scale makes me feel good too.
Apathy to government corruption + social & financial control of their populations is killing this world. From Belize to USA, EU and back albeit different degrees and prevalence.
Belize is, sadly, taking things to the next level by the looks of things. To say the least.
Making a stand as you have merits an enormous amount of respect and you most certainly have mine.
Stay safe.
Good Luck in the New Year John … this is some serious shit you are revealing.
Cheers … enjoy your vacation.
How fortunate we are to have people in our world like John. If we all had to depend on people like you”@everyday people, nothing would happen, there would be no invention, no creativity, no progress, no life. Anyone in history who has created something great, has been thought by the masses to be crazy. Now we all benefit from their craziness. John has unbelievable courage, wisdom that we cannot yet understand and has and is still creating something important. If you, Mr. everyday people, have such a busy life, what are you doing here..get on with it. Get out of your leather lazyboy and change the channel or in your case, just use the remote.
I can’t imagine that the U.S. intelligence agencies haven’t had a whiff of this already – the old worry that you’d be screwing up an ongoing investigation is always there – did you attempt to contact them? On the other hand there are arguments to blow it all out in the open too.. and I actually prefer this option that you seem to have chosen. Just hope the masses can handle it.
John might be crazy according to many, what about the evidence and news links , are they crazy ?
Where there’s smoke there’s fire. THANK YOU JOHN FOR SAYING WHAT OTHERS CANT
@everyday people…please don’t assume you speak for all of us, ie: “we’re busy….”. Some of us can actually handle our lives and still have time for other interests like Johns story. So, sorry for your inabilities, but Buh Bye.
Firstly I don’t believe John would do this for his SAFETY. It would be done to seek justice to those who hurt the people around him, himself that he loves.
USA as a country, as governmental control up their ass know it all continent irks me no end. I have followed many political adversaries, Alex Jones to Obama being in office.
Forgive me for being European & I can only see likeness in the USA focus on the Middle East as a likening to many dictators over the years. Bush seemed to make a lot of close friends think & compare to Nazi & or Weimar Rallies.
I read a Tom Clancy book Easter last year (the course of Spring 2012) that talked about USA using the Middle East, Afghanistan etc as their focus when I see this more like the WWII, a war on 2 fronts. Does one need a distraction to put focus on Libya, Syria, total atrocities of Egypt to deliberatly not show Mexico, South America, the Carribbean, African & Morrocean/Spain influence of Mexico/Columbian future foot holds?
What bugs me is like people here, it’s going on, yet many don’t believe it. Wake up people. This makes me think a lot of the players of the Iraq & Gulf wars. Of Jordan, etc. So Chetchna, former Soviet & Arab speaking countries unite together vs Asia & Chinese financial power, vs Lebanon, Iran, Iraq, Kuwait? I start to feel USA counter spies eyes wanning. Yet EU & former Eastern ones are & were much better. If not still in place
Clancy showed this as fiction. Now John notes & shows how it’s connected. Also think hair dye. Hydrochloride as a chemical, used in mining & commercial industry/captalist powers.
Please if you read this don’t a) be niave to what’s around you. b) take what you read literally & at face value. I spent many years within photojournalism or photography aspects. people shock me by not knowing facts or actually sticking to the direct story yet thinking that investigative or reportative journalism, photography or photojournalism is is not not theories & speculation based.
Read between the lines. JFK here? John be well, i admire & think highly of you, no Wild Earp or Wiyde E Coyote here? Thank you & be safe.
That does not bode well for the People of the United Snakes.
Who are you speaking or? This guy is a self-made millionaire that has spent the last 20 years essentially doing whatever the hell he wanted. Many of us wish we could say that. Essentially, his life has been kickass. Why would he give a damn whether people like you respected him or not?
Castor Beans/Ricin are very dangerous. It does sound like a sinister plot… Get all the evidence out that you can now.
Aside from kathy griffin kissing anderson cooper’s dick on New years, here is proof that CNN is the most trusted source in news
http://www.youtube.com/watch?v=jTWY14eyMFg
Unless the US Gov’t has been aware of this for a while. It all seems so outlandish – Who are the Billboards in BZ Addressing..? The Common Citizenry, or the GOB..? It is safe to say that some American “Diplomat” (term used loosely) has been apprised of this Human trafficking that may include Dangerous (to the US) People.
Many Goverments will “Sell” Passports and Citizenship for a set price, especially to Retirees on Set incomes. They call it an “Investment” in the Government. Indeed.
Allows for situations such as the Ones detailed by JM above. Especially, when it Occurs 2 hours by Plane from US Soil.
If the US Gummint is not aware of this – JM’s Expose ought to catch their attention, and perhaps bring down Barrow and his Band of Crooks. Most likely to be replaced by another Band of Thieves.
I am glad that the Webmaster (Chad..?) is printing the contrary posts as well.
No Way the Mainstream Media will cover a Story like this with any sort of detail, or pardon me: Cojones… Only alternative Media will disseminate Information such as this. At least initially.
The CNN, MSNBC, FOX etc. Media Cabals are Cowards. They tell 1/10th of the story at best. Or ignore it totally.
Tools of the Gov’t, basically.
It’s like peeling the layers of an Onion. Appauling. And I sense that You are just getting started… I am not usually surprised, A Utopian but Jaded Dude like me rarely is.. Will be tuned to Alex Jones later. Peace JM… Looking Sharp and Quite Local wit’ da Ranchers’ gear, BTW.
@querrier, Yes, I agree. Our government needs to be on this now, welcomming John’s input and expertise. Hezbollah working with Las Zetas; we cannot afford to “sweep this under the rug” for the children we raise to live in fear, alongside their children…so yes, I will be writing letters today!
Belize will not get better untill it gets worse so lets get it done one time get it overwith aand get on with life here in a proper fashion. Yes, Barrow does owe John an apology, the least of it, and should step down as this is happening in his administration,
and the story does need to be taken up by the major media and I feel it will be as we all have friends and the internet to bring this to the attention of many. I sent a note to homeland security and the white house. Lets all do our part to make Belize a better place to live and keep the ball that John has so well started rolling for us.
@ everyday people, Really? you wish for John to fade into obscurity? Perhaps you just stumbled upon his blog…I doubt it.
I was under the impression that duty as an FSO in Belize was a walk in the park. Quite literally an FSO with a newborn child would prefer as next assignment. What in the hell happened down there!!?
Hello John, I almost choked on my coffee as I read this new information. Somebody in the White House needs to open their eyes to this information, and soon. Belize and Barrow owe you much more than an apology, after what you have endured and the things you have lost to them. I do hope somehow they realize the mistake they made by messing with the wrong person…Take good care of yourself!
You have interesting info, but there’s a problem. Your not exactly credible. You’ve pulled some pranks, left the country to avoid paying taxes and answering to some real and some rediculous law suits, you play with guns and your dating way out of your age range.
So, who’s listening to you?
You’re a smart guy, even better you’re clever, so why aren’t you looking for the right person to hear you?
I understand that you need to go public for your safety and the safety of those that got involved, but, why not a main stream semi-reputable news organization like CNN or MSNBC? Does this all go back to credibility?
My life doesn’t feel like a train wreck. It feels pretty good.
Amazing how you can do all of this and yet your life is still a train wreck..If you had put half as much thought into your life you could have been respected. Now quietly fade into obscurity john..we’re busy with real lives..
How does John gain compensation for the damages he has suffered? And how can corruption be reduced in Belize? All it takes is one US Federal Prosecutor to enforce USA Law, and John wins. Results would be the prosecution of corrupt Belize Authorities in US Criminal Court, and visas being cancelled for corrupt persons not criminally prosecuted. Why will the US Government not enforce the FCPA Federal Corruption Prevention Act, to prevent & punish all the illegal activities that John has exposed?
I support your exposure of govt corruption. I also applaud your use of cyber tools to infiltrate the human system. Unfortunately, these type of tactics are normally only used to expose large, rich nations follies. South America, especially Paraguay, is rife with corruption and terrorist safe-houses. If your travels keep you in the heartland much longer, please know that you have much admiration from the state of Iowa. Our doors are always welcome to truth-seekers.
Dude, this is beyond scary…run fast, run hard and stay hidden. This is NSA stuff and the Mexican Cartels don’t mess around…Praying for you my Friend…Really am…BTW, hopefully Sam is far away from the reach of the Mexicans as well…AND the other groups…including the US Gov….Scary
Odd that consular McCarthy has departed Belize and is currently in Arlington.
Meanwhile they raided him for running an illegal antibiotics lab… that is absolutely insane. If he was even remotely working on a topical anesthetic they should have thanked him. First world problems equate to the power going out for 2 seconds because everyone turned their air conditioner on at the same time. In these countries, there is serious corruption where lives are lost in power struggles. Power over money, information, and people. At the very least, there is a laundering scheme and a human trafficking scheme going on in Belize and in other Central American governments. And that is at the very least.
Thanks for the efforts and the info John. Hopefully now that Obama Latin America La gets expanded to include this aspect as well as the Iran one.
Hopefully, 2013 brings some brightness into you and Sam’s and Amy’s lives.
Instinctively, John, if it looks and smells like something, it probably is (no pun intended with the link there). When the PM of Belize literally called one of its citizen “bonkers” on live international television, I knew that something was seriously wrong with that country and their cover story. I do not know for how long you have been unraveling this new evidence, but if caution is left to the wind, it could be disastrous for any number of people here in the states or even in Central and Latin America. It is better to get the word out now that these things are going on. People go to these resorts in Mexico, Honduras, Belize, and any number of Central American countries and often do it willfully, knowing full well that their entire safety would be compromised if they left the comfort of the resort and that there are literally people starving a hundred yards away. I don’t pretend to have all the answers, but I suspect your evidence is significant enough to at least justify some kind of investigation. I can’t help but say that I noticed with absolute horror on your CNBC interview awhile ago that when you mentioned people are kidnapped, murdered, and go missing in countries like Mexico and Honduras, everyone knows it could happen, but why not in Belize? This rhetorical question seemed to have the interviewers dumbfounded, as if they had no knowledge of the outside world whatsoever. I hope you intend to make this info public on the Alex Jones interview, or perhaps you already have. Good luck
Thank you John, Hope the U.S. awakens very soon. Always awaiting next instalment. Now we wait and see.
I like your style, I hope you get your revenge and vindication, hey what happened to your house and stuff ? Can you have your stuff shipped to you here in states ? Just curious never was a big fan of leaving the states for the reasons that happened to you wondering how to protect assets.
People who are paying $25,000 to enter the U.S.A illegally are not planning to work at Mcdonald,s . The fact that no mass arrests have been made indicates the authorities are asleep at the wheel,don,t want to speculate what 1200 terrorists are capable of.
Could also be this:
http://www.google.com/patents?id=px5PAAAAEBAJ&printsec=abstract&zoom=4#v=onepage&q&f=false
Well ,there should be no doubt now to your claim that you would be killed by belize authorities.Imagine 10 TERRORISTS A MONTH for ten years entering the U.S.A = 1200 Terrorist now residing in the states,serious stuff.
I am sick to my stomach. I knew something was weird when I saw all the billboards, but had no idea the extent of it. You are amazing John. Thank you for all that you do to make this world a better place.
“H2SO4: Sulfuric acid is a highly corrosive strong mineral acid with the molecular formula H2SO4. It is a colorless to slightly yellow viscous liquid which is soluble in water at all concentrations.”
“CCL4 may refer to Carbon tetrachloride. Carbon tetrachloride has practically no flammability at lower temperatures. Under high temperatures in air, it forms poisonous phosgene. Exposure to high concentrations of carbon tetrachloride (including vapor) can affect the central nervous system, degenerate the liver[10] and kidneys[12] and may result (after prolonged exposure) in coma and even death.”
“Routine operations at the former Rocky Flats Nuclear Weapons Plant frequently involved the use of the chemicals carbon tetrachloride and beryllium.”
“Carbon tetrachloride is insoluble in water, but miscible with alcohol, benzene, … It was used as a chemical warfare agent in WWI…”
“Ricin is easily purified from castor oil manufacturing waste. The aqueous phase left over from the oil extraction process is called waste mash. It would contain about 5–10% ricin by weight, but heating during the oil extraction process denatures the protein, making the resultant seed cake safe for use as animal feed. From fresh seed, separation requires chromatographic techniques similar to other plant proteins.”
These two compounds are known to also be used in the manufacturing of cyanide blood agents: http://books.google.com/books?id=4pwMQM3PuyoC&lpg=PA340&dq=%22Carbon%20tetrachloride%22%20chemical%20weapon%20%22Sulfuric%20acid%22&pg=PA340#v=onepage&q=%22Carbon%20tetrachloride%22%20chemical%20weapon%20%22Sulfuric%20acid%22&f=false
Yes, ricin.
John, please stay safe. God Bless.
Any way to get someone in Washington, DC to start paying attention to this stuff? Besides it hitting the wire as “crazy John McAfee claims X Y Z…”. Unless they already know about it. Extracting oil from plants sounds odd… someone mentioned ricin but could also be coca extract… I have no idea. Something sinister is going on here.
ricin?
WOW this is crazy…. Thank you John
YES/…. Lets go
Thats deep.
..this is nice stuff – i knew someone high up there in the government had given orders for Arthur Young to be killed – i hope you spill all the truth soon. Good work there!!